Offensive SecurityThat Proves Exploitability —Not Just CVE Lists
WhiteHawk's offensive security module simulates real-world attackers against your environment. Our offensive security team holds OSCP, OSWE, OSEP, OSWP, CEH, CRTP, C|PENT, and GPEN certifications and has run engagements against banks, fintechs, museums, and healthcare networks across MENA.

Defensive Security Solutions
Our Defensive Security Solutions combine human-led SOC operations with AI-driven correlation, automated containment, and continuous Threat Hunting. Every component reduces mean-time-to-respond without flooding your team with low-fidelity noise - cyber defense at MENA scale.
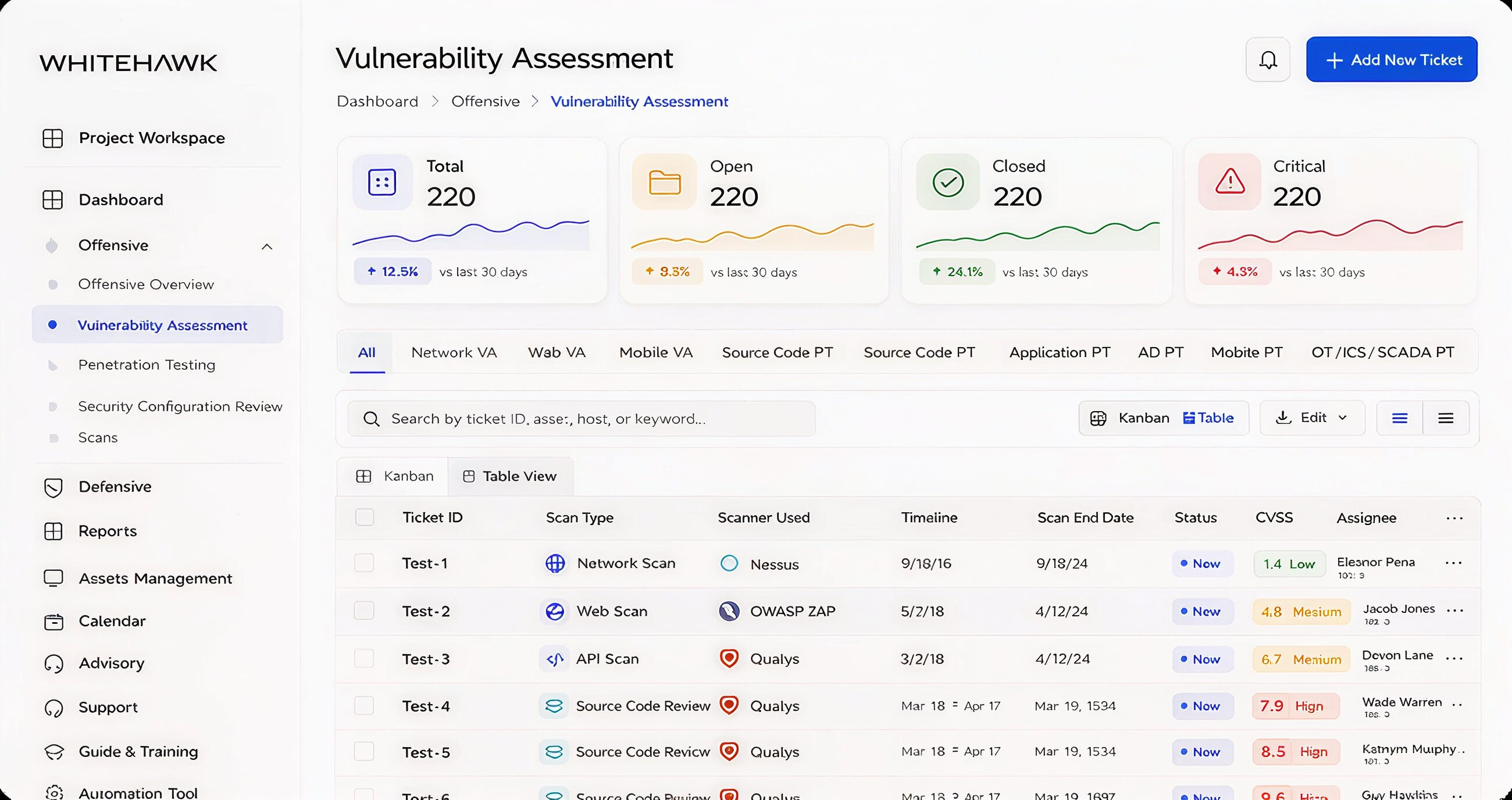
Vulnerability Assessment
Vulnerability Assessment maps every weakness across your attack surface - applications, infrastructure, cloud workloads, and identity layers - then proves which ones are actually exploitable in your specific environment, the foundation of any offensive security program.
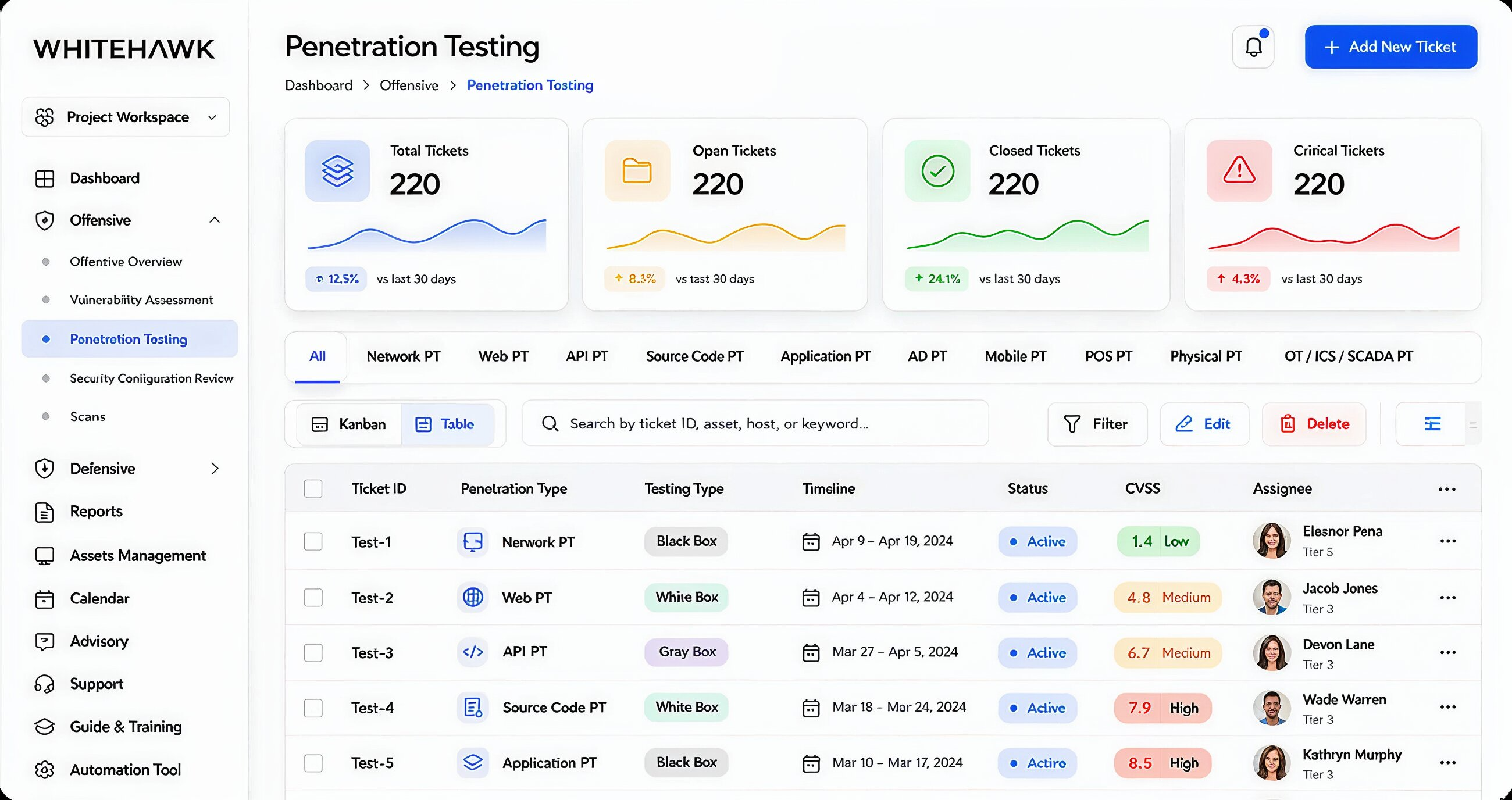
Penetration Testing
Penetration Testing is authorized, hands-on simulation of a real attack against your systems. WhiteHawk pen testers chain vulnerabilities the way adversaries do, exposing the realistic blast radius of every weakness across your stack.
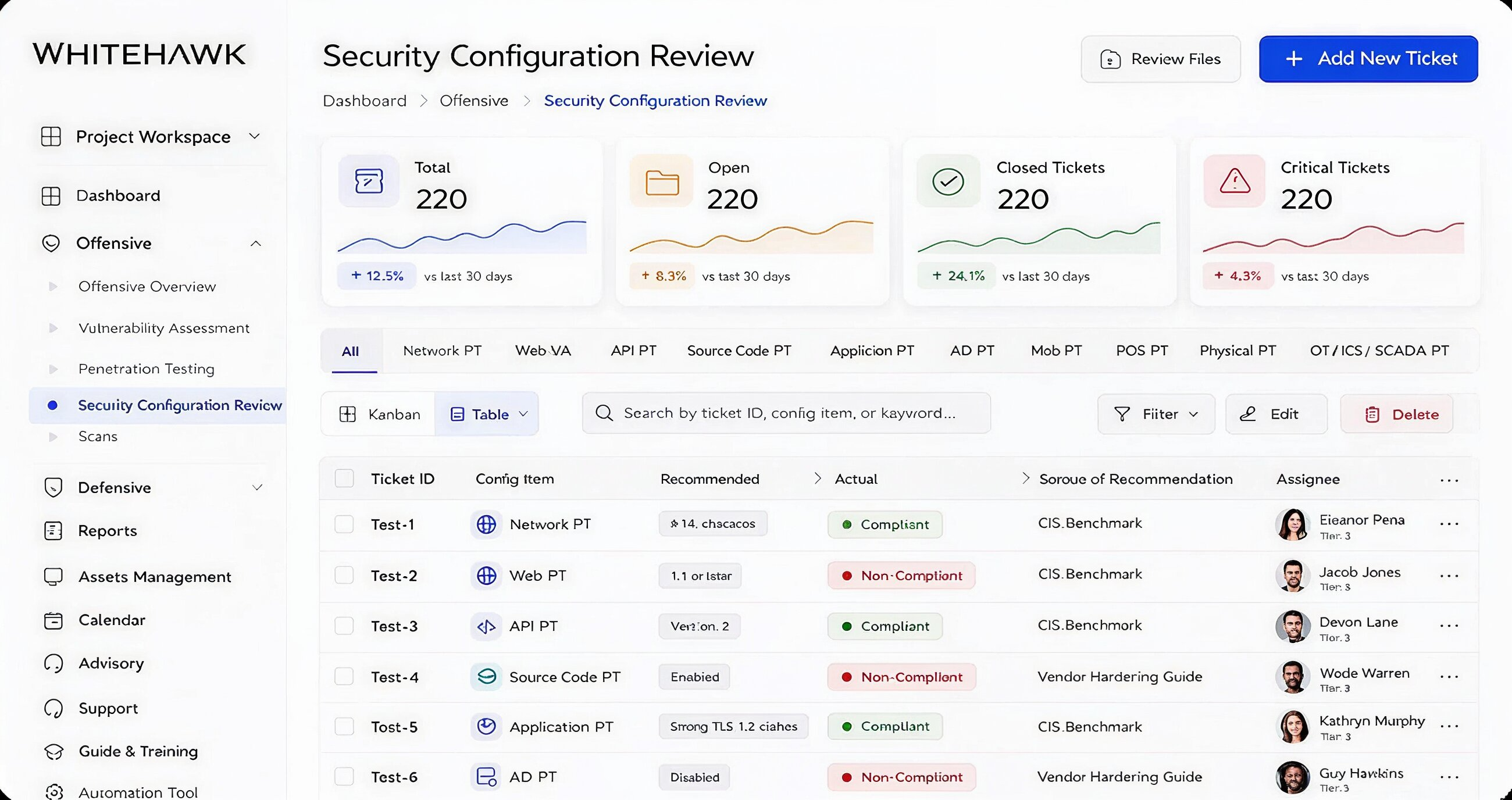
Security Configuration Review
A security configuration review validates that your firewalls, cloud accounts, identity providers, and operating systems are hardened against known misconfigurations - the silent root cause behind most breaches uncovered by offensive security engagements today.
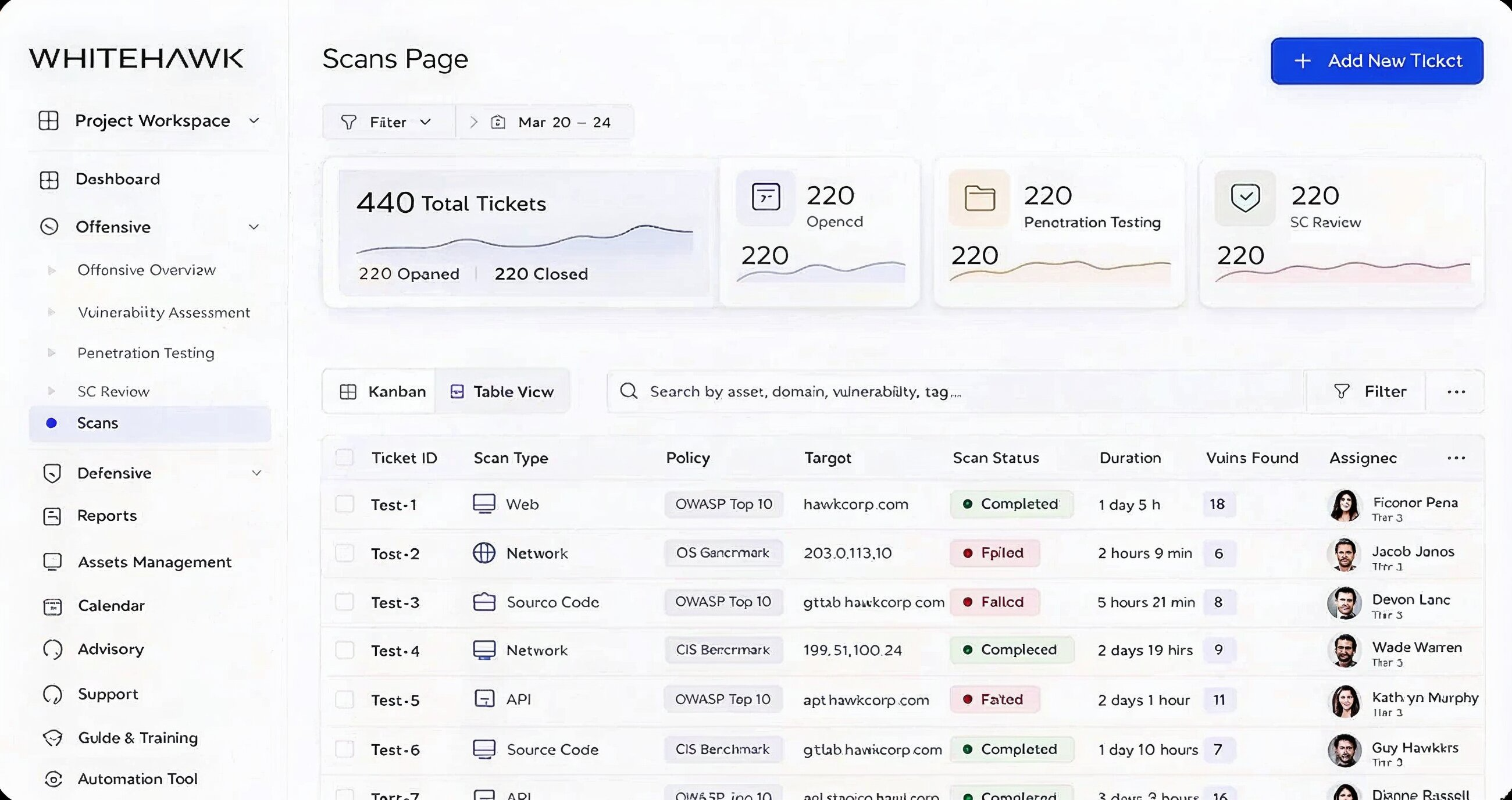
Automated Security Scans
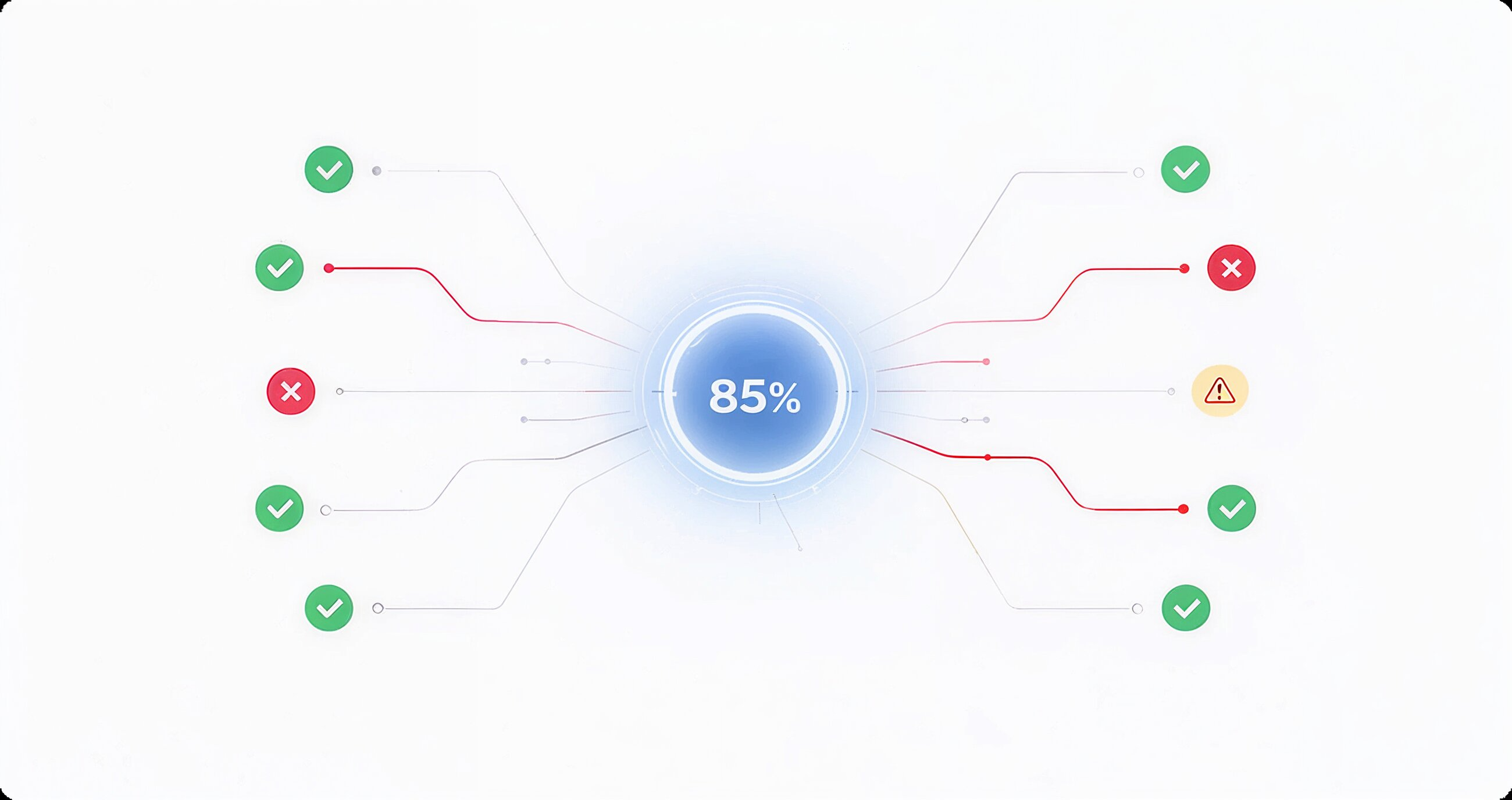
Continuous, automated security scans run inside the WhiteHawk platform around the clock. New assets, new code, and new exposures are flagged in real time and routed to the right team automatically.
CIS Benchmark Assessment
Our CIS benchmark assessment measures servers, workstations, and cloud workloads against the Center for Internet Security baseline - the same standard auditors use to score security maturity, integrated with our offensive security findings.
Ticketing and Reporting
Every Vulnerability Assessment finding becomes a ticket with an owner, severity, business impact, and step-by-step fix. Reports come in two layers: technical depth for engineers and an executive view for boards.

Frequently Asked Questions
A quick answer to the most common platform comparison question